When was the last time you sat down with your team to update your industrial control system (ICS) security risk assessments? If you’re like most organizations, the answer is probably “not recently enough”. The reality is stark: the complexity of modern ICS environments combined with constantly evolving cyber threats means that manual risk assessment processes have become a bottleneck—time-consuming, error-prone, and difficult to keep up-to-date.
Here’s the challenge: Your organization needs to align with ISA/IEC 62443-3-2 standards. You’ve got critical assets scattered across multiple security zones. New threat intelligence arrives constantly through MITRE ATT&CK framework. Your risk scenarios need to map to real-world attack techniques, mitigations, and adversary profiles. And after all those enrichments, you still need to export everything back into a structured Excel workbook that preserves your existing data and adds actionable intelligence.
Running this process manually? That’s typically a week-long project. Running it quarterly? Practically impossible.
Enter ICS ThreatWeaver—a powerful, open-source web application that transforms your risk assessment workflow from a manual marathon into an automated, intelligence-driven process. In this comprehensive guide, we’ll explore what ICS ThreatWeaver is, why it matters, how it works, and how it can revolutionize your approach to industrial cybersecurity risk management.
What Is ICS ThreatWeaver?
ICS ThreatWeaver is a FastAPI-based web application designed to automate the ISA/IEC 62443-3-2 Detailed Risk Assessment (DRA) process by leveraging the power of MITRE ATT&CK for ICS.
In practical terms, users can start with the built-in starter workbook provided by ICS ThreatWeaver (or supply their own ISA/IEC 62443-3-2 workbook). The system then enriches each relevant row with canonical MITRE ATT&CK for ICS data, including technique IDs, tactics, mitigations, and adversary context, and generates a structured output workbook that preserves original content while adding actionable threat intelligence.
Real-World Relevance
Industrial control systems power the infrastructure we depend on: power grids, water treatment facilities, manufacturing plants, and critical infrastructure. These systems face unprecedented cyber threats. The gap between threat landscape awareness and risk assessment accuracy has widened considerably. Organizations need to:
- Map their assets to real attack techniques
- Understand which adversary profiles threaten their systems
- Identify the right mitigations aligned with industry frameworks
- Document everything in a defensible, auditable format
ICS ThreatWeaver bridges this gap by automating the integration of threat intelligence into your risk management framework.
Why ICS ThreatWeaver Matters
The Pain Points it solves:
1. Risk Assessment Delays
Traditional manual risk assessments in ICS environments can take weeks. Teams spend countless hours manually:
- Cross-referencing attack techniques against their assets
- Looking up mitigations and adversary classifications
- Copying and pasting data between multiple spreadsheets and databases
- Verifying mappings and maintaining version control
- With ICS ThreatWeaver, this entire workflow is compressed into minutes.
2. Inconsistency and Human Error
When techniques are mapped manually, inconsistencies inevitably creep in. One analyst might interpret “control server” differently than another. Mitigations might be missed. Reasoning for mappings disappears—making future maintenance and audits difficult.
3. Outdated Threat Intelligence
The MITRE ATT&CK for ICS matrix evolves continuously. New techniques are added. Existing techniques are modified. Your risk assessments can quickly become outdated without a systematic way to track and import the latest threat intelligence.
ICS ThreatWeaver fetches the latest MITRE dataset directly, tracks which techniques are new or modified, and tags everything with version information for full traceability.
4. Lack of Standardization
Different teams might structure their Excel workbooks differently, use different asset naming conventions, or organize zones in incompatible ways. ICS ThreatWeaver enforces a standardized workflow while preserving your existing column headers and structure.
5. Compliance and Auditability
Regulators and auditors want to understand why you mapped a given scenario to a particular MITRE technique. ICS ThreatWeaver maintains a full audit trail—including change logs, original snapshots, and mapping justifications—so your risk assessments are defensible and compliant.
Who Should Use ICS ThreatWeaver
- Critical infrastructure operators managing power, water, oil & gas, or telecommunications systems
- Regulatory compliance teams implementing ISA 62443 frameworks
- Cybersecurity teams in manufacturing and industrial environments
- Risk management professionals responsible for ICS asset inventories and threat modeling
- Consultants advising on industrial cybersecurity strategies
- Organizations undergoing audits that require detailed risk documentation
Core Features of ICS ThreatWeaver
1. Live MITRE ATT&CK for ICS Integration
What it does: Automatically fetches the latest MITRE ATT&CK for ICS dataset directly from MITRE using STIX bundle imports, with complete version tracking.
Why it matters: The threat landscape evolves constantly, so your risk assessments must reflect today’s adversarial behavior, not last year’s. By pulling live data, you ensure your assessments are always current.
Example use case: Your organization performs its annual risk assessment in January. A new critical ICS attack technique is published by MITRE in March. Rather than waiting until next year’s assessment or performing a costly manual update, ICS ThreatWeaver’s versioning system allows you to import the new dataset and immediately see which techniques are new or modified.
Key capabilities:
- Direct STIX bundle import with one-click updates
- Per-import version tagging and full historical tracking
- Detection of newly added and modified techniques between versions
- STIX-derived technique-to-asset relationship extraction
2. Rule-Based Mapping Engine
What it does: Applies deterministic, keyword-based rules to automatically map MITRE techniques to your industrial assets (PLCs, HMIs, field controllers, etc.).
Why it matters: Instead of guessing which assets are vulnerable to which attacks, the engine uses proven heuristics to suggest the most relevant assets for each technique. This dramatically reduces manual work while maintaining consistency.
Example use case: You have 83 MITRE ICS techniques to map to your 18 asset types. The mapping engine runs in seconds, producing ranked asset candidates for each technique with explicit reasoning. An analyst reviews and approves them, and you have a complete, documented mapping framework.
Key capabilities:
- Automatic asset suggestion with confidence scoring
- Human-readable reasoning for each suggestion (e.g., “keyword match: ‘HMI’, ‘operator’, ‘display'”)
- Analyst approval workflow for overrides and customization
- Per-mapping metadata including confidence, justification, and version stamps
3. Custom Assets & Security Zones
What it does: Allows you to define site-specific assets beyond MITRE’s canonical taxonomy and organize them into ISA/IEC 62443 security zones.
Why it matters: The MITRE asset catalogue is comprehensive but generic. Many ICS environments include vendor-specific, model-specific, or site-specific equipment. ICS ThreatWeaver helps standardize mapping to MITRE assets for consistent analysis and traceability.
Example use case: You run three security zones: DMZ, Production Process, and Field Devices. Within each zone, you have a mix of MITRE-standard assets (PLCs, RTUs) and custom equipment (legacy Supervisory computers from vendor X, specialized safety controllers). You define these custom assets, map them to MITRE asset families, and then create a zone-specific threat matrix showing exactly which MITRE techniques apply to your exact environment.
Key capabilities:
- Custom asset registry with vendor, model, and description fields
- Many-to-many mapping from custom assets to MITRE asset families
- Security zone creation and management aligned with ISA 62443 zoning
- Per-zone threat matrix with automatic deduplication across direct and mapped assets
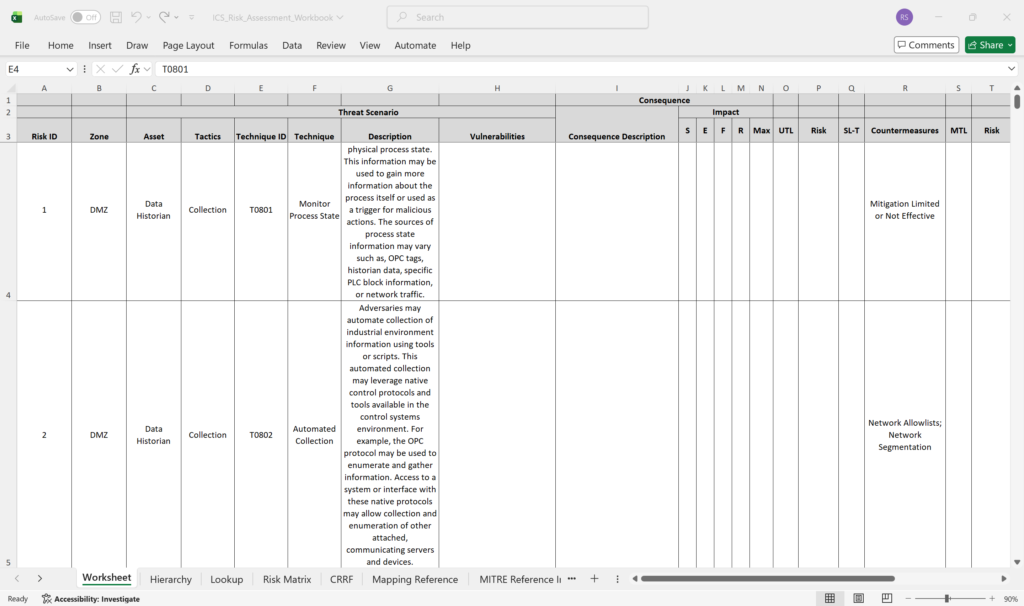
4. Threat Matrix Visualization & Excel Export
What it does: Generates dynamic threat matrices showing which techniques apply to which assets, and exports everything to populated Excel files with macro preservation.
Why it matters: Threat matrices are the lingua franca of risk communication. Exporting to Excel with preserved macros means your existing dashboards, VBA scripts, and automation continue to work unchanged.
Example use case: Your security operations team uses a custom Excel dashboard with VBA macros that calculate risk scores and generate charts. ICS ThreatWeaver exports the threat matrix to your .xlsm template, preserving all your existing macros and named ranges. Your dashboard immediately reflects the new threat intelligence without any rework.
Key capabilities:
- Per-zone threat matrix generation with row deduplication
- Direct browser download of .xlsx or .xlsm files
- User-supplied template upload (bring your own Excel template)
- VBA macro preservation throughout the transform pipeline
- High-fidelity Excel output suitable for regulatory submissions
How ICS ThreatWeaver Works: Logic & Architecture
Think of ICS ThreatWeaver as a guided workflow where each step builds on the previous one. You move from importing threat data, to organizing it, to applying it, to exporting results.
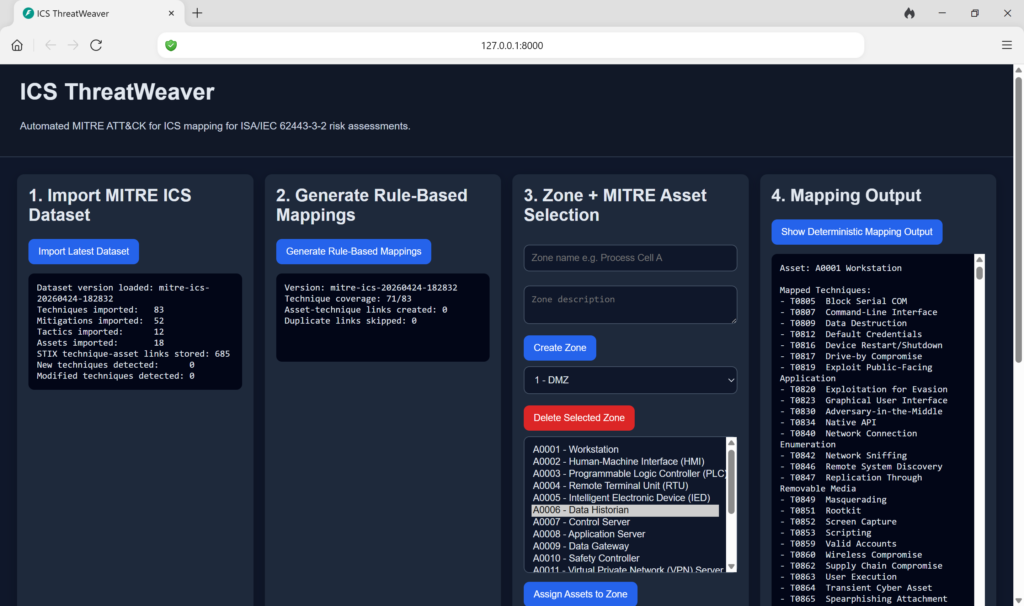
Step 1: Import MITRE ICS Dataset
- User clicks “Import Latest Dataset”
- System fetches the latest MITRE ATT&CK for ICS STIX bundle
- New techniques are detected and compared against the previous version
- Dataset version is tagged and stored
Step 2: Generate Rule-Based Mappings
- User clicks “Generate Rule-Based Mappings”
- System applies deterministic keyword rules across all MITRE techniques
- Mapping suggestions are created linking techniques to asset types
- Deduplication logic consolidates redundant mappings
Step 3: Zone + MITRE Asset Selection
- User creates security zones (e.g., Process Cell, Field Devices, DMZ)
- User selects which MITRE assets belong to each zone
- Zone definitions become the context for threat analysis
Step 4: Show Deterministic Mapping Output
- User clicks “Show Deterministic Mapping Output”
- System displays the rule-based technique-to-asset mappings with reasoning
- Analyst can review suggestions for accuracy and context
- Mappings are tagged with confidence and justification
Step 5: Generate Zone Matrix
- User selects a zone and clicks “Generate Zone Matrix”
- System calculates all applicable techniques for that zone’s assets
- Deduplication removes redundant entries
- Zone-specific threat view is displayed
Step 6: Excel Export
- User selects output filename and optional template
- Clicks “Download Populated Workbook”
- System generates populated Excel file with threat matrix
- File is streamed to browser for download
Download from GitHub
Want to try ICS ThreatWeaver on your own system? The fastest path is to download it directly from GitHub and run it locally.
Conclusion
ICS ThreatWeaver brings together three critical capabilities: automation, intelligence, and compliance. It transforms risk assessment from a once-per-year manual slog into an agile, intelligence-driven process that you can run quarterly, monthly, or even more frequently as threat conditions change.
For industrial cybersecurity professionals, the value is clear. You get current threat intelligence embedded in your risk register. You get defensible, auditable assessments that satisfy regulators. You get back the time your team was spending on manual data entry and instead channel it toward strategic risk decisions.
Whether you’re a water utility ensuring compliance, a manufacturing consultant supporting clients, or an energy company managing critical infrastructure, ICS ThreatWeaver is a powerful ally in your cybersecurity arsenal.
Ready to modernize your ICS risk assessment workflow? Explore ICS ThreatWeaver today, and discover how automation can strengthen both your security posture and your compliance position. Visit advanceleap.com to learn more about this project and other resources for industrial cybersecurity excellence.
FAQs
1. What is ICS ThreatWeaver and how does it differ from manual risk assessment?
ICS ThreatWeaver is an automated web application that enriches ISA/IEC 62443-3-2 Detailed Risk Assessment workbooks with threat intelligence from the MITRE ATT&CK for ICS matrix. Unlike manual assessment—which involves hours of cross-referencing techniques, assets, and mitigations—ICS ThreatWeaver completes the process in minutes. It applies consistent, rule-based logic to every row, maintains a full audit trail, and keeps your data synchronized with the latest threat intelligence. The result is faster, more consistent, and more defensible risk assessment.
2. Does ICS ThreatWeaver preserve my existing Excel workbook structure and data?
Yes, absolutely. ICS ThreatWeaver treats your existing DRA workbook as the source of truth. All original columns, headers, and data are preserved exactly as written in the output. The system adds five new sheets with enrichment data (Enhanced Risk Assessment, Mapping Reference, MITRE Reference Index, Change Log, and Original Snapshot), but nothing is deleted or modified. This means your existing Excel formulas, macros, and dashboards continue to work without any rework.
3. How often should we update our risk assessments using ICS ThreatWeaver?
The frequency depends on your operational needs and regulatory requirements. Many organizations run updates quarterly to capture MITRE’s regular releases. Others update monthly for continuous threat monitoring. The beauty of ICS ThreatWeaver is that the automated nature makes frequent updates feasible—what might take a week manually now takes minutes. We recommend at least quarterly updates to stay aligned with evolving threats, but your organization may choose a different cadence based on risk appetite and compliance requirements.
4. Can ICS ThreatWeaver handle custom assets that aren’t in the MITRE catalog?
Yes. ICS ThreatWeaver includes a custom asset registry where you can define site-specific equipment (vendor-specific models, legacy systems, specialized controllers) that aren’t in the standard MITRE ATT&CK for ICS asset catalog. Each custom asset is linked to one or more MITRE asset families with documented justification. This allows you to tailor the mapping engine to your exact environment while maintaining alignment with industry-standard threat intelligence.
5. What security features does ICS ThreatWeaver include to protect sensitive risk data?
ICS ThreatWeaver implements several production-grade security controls: SSRF guards validate all outbound URLs, path-traversal validation ensures file access stays within approved directories, per-IP rate limiting prevents abuse, optional API-key authentication protects state-modifying endpoints, and comprehensive logging provides a full audit trail. These features ensure your sensitive risk assessment data stays confidential and your system stays reliable, meeting the security requirements of critical infrastructure environments.



how to get this tool